Designing Secure Protocols for Wireless Sensor Networks
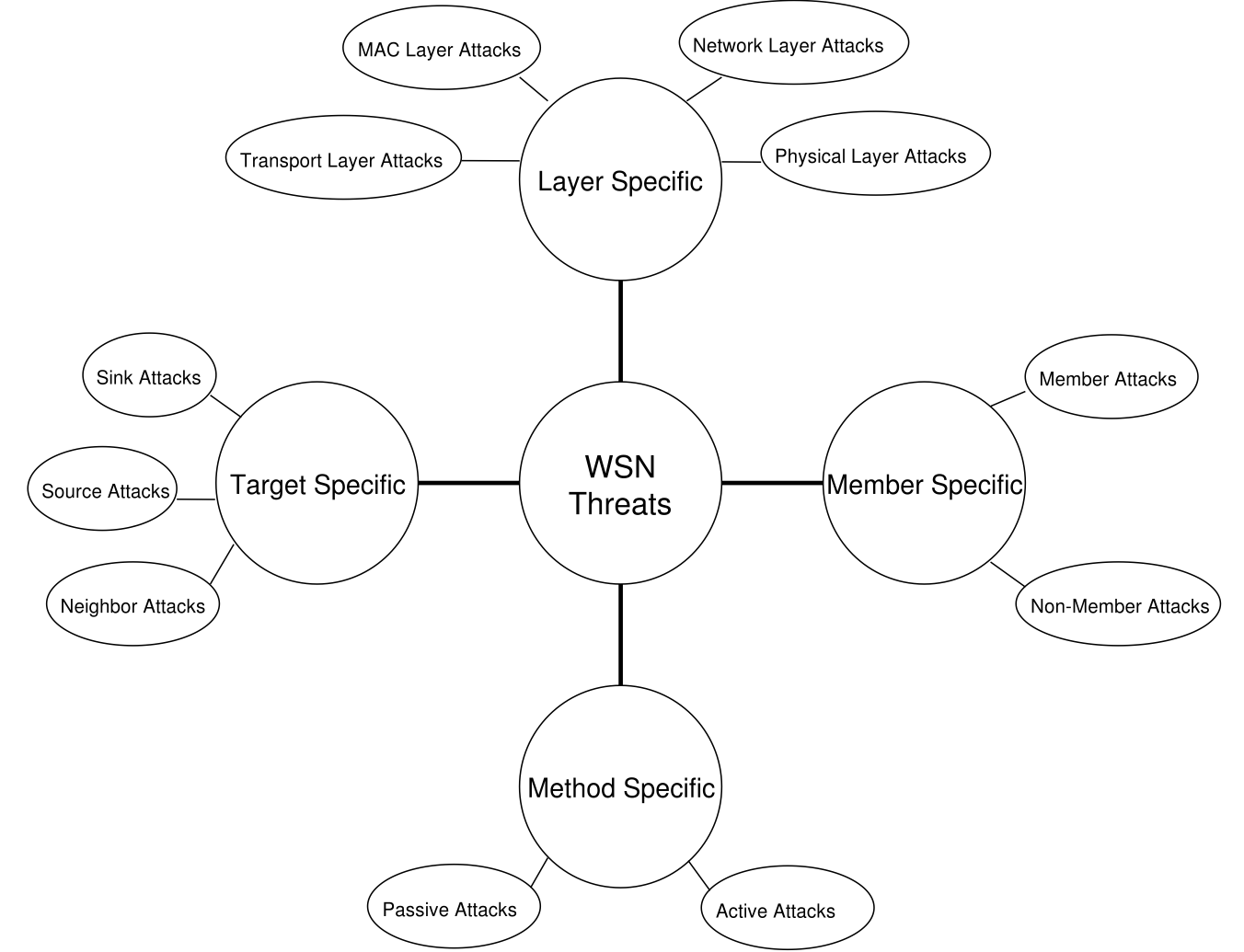
Over the years, a myriad of protocols have been proposed for resource-limited Wireless Sensor Networks (WSNs). Similarly, security research for WSNs has also evolved over the years. Although fundamental notions of WSN research are well established, optimization of the limited resources has motivated new research directions in the field. In this study, we seek to present general principles to aid in the design of secure WSN protocols. Therefore, building upon both the established and the new concepts, envisioned applications, and the experience garnered from the WSNs research, we first review the desired security services (i.e., confidentiality, authentication, integrity, access control, availability, and nonrepudiation) from WSNs perspective. Then, we question which services would be necessary for resource-constrained WSNs and when it would be most reasonable to implement them for a WSN application. We also introduce a new threat model, called Target-Based attacks as a complementary threat model to the current literature.
- A. Selcuk Uluagac, C. P. Lee, R. A. Beyah, and J. A. Copeland, “Designing Secure Protocols for Wireless Sensor Networks,” in Proceedings of the 3rd International Conference on Wireless Algorithms, Systems and Applications (WASA), Dallas, Texas, October 2008 (also available in Lecture Notes in Computer Science (LNCS) 5258, Springer-Verlag, pp. 503-514, 2008), [bibtex],[pdf]



